With as many businesses as there are currently accessing, using and storing data in the cloud, it is essential that security is a key feature that your business is both aware of and deploying to protect your data.
Many have argued that we are now creating data faster than we can store and use it. The global cloud computing market is expected to grow by more than 17% between 2020 and 2025. It is worth billions of dollars and it’s growing all the time. Your business is likely to access either software or storage in the cloud and it is vital that you are aware of your cybersecurity in relation to this.
Cloud security is the set of mechanisms that are designed to protect cloud-based applications, data and infrastructure. They do this by ensuring the authentication of those accessing the data and devices, protecting privacy and controlling access to resources. Increasingly, companies are placing the responsibility for the security of their cloud services and applications with IT professionals. However, there are possibilities to bring the skills in-house through professional digital cloud training, which will include information and training on cloud security.
Cloud Security Is a Necessity for all
As cloud computing and storage become part of our day-to-day lives and integral to daily business, customers are becoming more demanding of secure and safe services. Ensuring the safety and security of data and users’ information is key to building trust, and cloud services offer excellent infrastructure to embed security controls in a consistent and layered fashion. Whether you are providing that security within your own IT department, or bringing in a service provider, there are some key things to look for. Well, you can go for the services of a local Cloud migration provider here in Newark CA, by the name of “Dataknox” that offers swift, easy, seamless and hassle-free migration to Cloud storage from a physically located data server. So, you need to look into these below-mentioned key aspects, before choosing the services of one such Cloud services company.
Data encryption ensures that data is converted from a readable format into an encoded format that can only be processed after it is decrypted. This scrambling of the data makes it unreadable to anyone without the right encryption key and is important to ensure data confidentiality.
Authentication processes should be strong and include multi-factor authentication (MFA), which allows users to authenticate who they are by providing evidence of their identity through multiple pieces of evidence. With many breaches occurring because of compromised passwords, MFA ensures greater security for your data and applications.
Threat detection ensures the security of your cloud and data ecosystem by analyzing activity across the entire network and detecting malicious activities. Key to any threat detection practice is ensuring mitigation efforts are in place and easy to implement so that any threat that is detected can be neutralized before any data or applications are compromised.
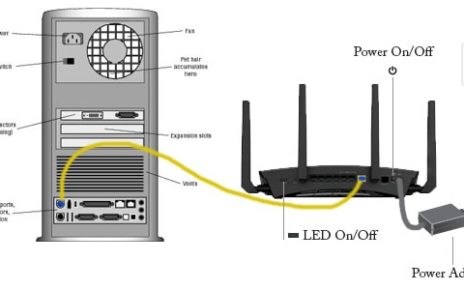
Regardless of how you are ensuring the security of your cloud-based platforms and data, it is essential to put in place key security measures early in the process of adoption and expansion. Ensure all your staff members understand any points of weakness before they become targets. Knowing your organization’s infrastructure and where weak points might be by having a holistic understanding of the system is the first step.
Remember that most data breaches occur as a result of human error, so maintaining a strong cloud storage position from the outset will eliminate any possible errors and breaches.